Autor
Najnowsze
Archiwum
Extracting SSH Private Keys from Windows 10 ssh-agent
Linux Reverse Engineering CTFs for Beginners
Visual Analysis with ProcDOT
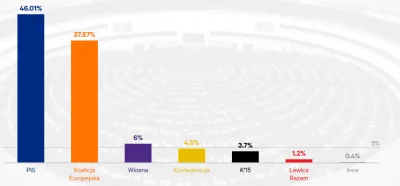
#polanowyhacking
Linux Reverse Engineering CTFs for Beginners
Visual Analysis with ProcDOT
#polanowyhacking
Prevent email hacking by taking these three important steps
Intel SGX 'safe' room easily trashed by white-hat hacking marauders: Enclave malware demo'd
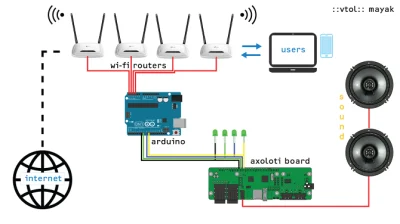
New Offensive USB Cable Allows Remote Attacks over WiFi
Web Security 101 - Insecure Direct Object Reference - You are who you say you are, right?
#polanowyhacking
Intel SGX 'safe' room easily trashed by white-hat hacking marauders: Enclave malware demo'd
New Offensive USB Cable Allows Remote Attacks over WiFi
Web Security 101 - Insecure Direct Object Reference - You are who you say you are, right?
#polanowyhacking

DNSGrep — Quickly Searching Large DNS Datasets
How to break into NullByte Machine - CTF Writeup
https://maldroid.github.io/
Pwny Race - Test Session - patrz filmik
#polanowyhacking
How to break into NullByte Machine - CTF Writeup
https://maldroid.github.io/
Pwny Race - Test Session - patrz filmik
#polanowyhacking





Hotspot Analysis:Regional rivalry between India-Pakistan: tit-for-tat in cyberspace
File upload vulnerability scanner and exploitation tool.
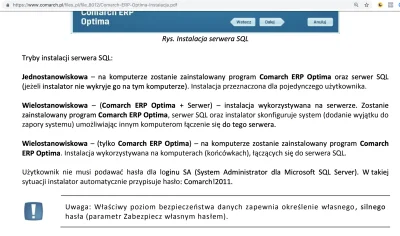
DNS